Typosquatting

Typosquatting. It’s a funny word, with not so funny implications.
Typosquatting is a term used when scamming companies purchase domains with typos that look similar to the correctly spelled domain name. Ever type in a web address incorrectly? Don’t be surprised if a pop up opens on your screen. This method of data invasion is simple to step into, and with the right tools you will be prepared to step out just as easily. There are different variations and different levels of severity when dealing with typosquatters. Let’s take a look at how it happens.
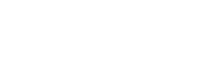
You go to your favorite retailer’s website in search a gift for your nephew’s birthday, we’ll use Walmart for example. You type in: www.Wallmart.com. Catch the typo? You may be faced with a webpage that looks nothing like you expected. (see image 1) In reading the displayed message, one could come to believe that it is a truly legitimate effort by “Microsoft” to keep your browsing experience safe. Just to be safe, you call “Microsoft.”
On the phone, you will be greeted by a “Certified Microsoft Technician” giving you clear directives for you to follow. They appear caring and alarmed at the predicament you have stumbled into. The “technician” will then attempt to gain remote access to your machine.
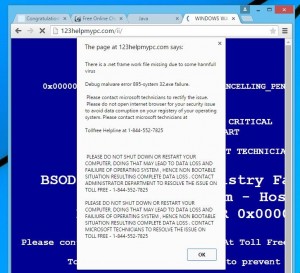
Once given entry, the technician will run a scan of your system and display the results on your screen. (see image 2) Other times they ask you to participate and direct you to visit illegitimate websites which download malicious software. Here’s where they hope to scare you into reaching for your wallet. The results pulled will be filled with malware and registry key errors that are NOT actually resting in your computer.
The illusion of these “computer infections”, gives them the opportunity to sell you a phony solution and additional annual services. Charges are typically from a few hundred dollars to much more, but no real services are provided. Sadly, you’re out hundreds of dollars, there is no issue present, and sensitive data may have been compromised. Not to mention you still haven’t gotten a gift for your nephew.
You don’t have to be a victim.
There is hope:
- Be careful and take your time: It’s easy to get a little lazy when typing in a website URL that you visit regularly. The bad guys are hoping that you have a slip of the finger and add an extra “L” in Walmart.
- Not a windows contact method: Rarely does Microsoft communicate with its customers in the mannor of an anonymous pop-up.
- What to listen for: (microsoft.com)
- Windows Helpdesk
- Windows Service Center
- Microsoft Tech Support
- Microsoft Support
- Windows Technical Department Support Group
- Microsoft Research and Development Team (Microsoft R & D Team)
If the individual says they are calling you from Microsoft or Windows, hang up!
- Don’t give your password and user name: Your user name and password are personal and should not be given away. Change your password immediately if you have unknowingly shared it. Scammers ask for your password and username for further intrusions on later dates.
- Don’t Pay: Do not give any credit card numbers to anyone claiming to be Microsoft or an unknown “tech support” company. The technician will want your card over the phone in order to immediately charge it.
- Close it: If you ever experience one of these popups:
- Attempt to close the window
- Hover your mouse over the browser icon on your task bar, right click and select close window
- Turn off your workstation and reboot your machine.
- Whatever you do, DON’T GIVE THEM ANYTHING!
- Trust your gut: If you feel uneasy, stop! Trust your instincts and proceed no further.
Typosquatting and the illegitimate pop ups are easy to stumble upon. By being prepared and exercising caution you can avoid the cost and loss of privacy caused by these illegal sites.